We are not unfamiliar with the term "hacking." They are primarily known for obtaining unauthorized access to a person's or organization's computer system and resources for personal gain. In general, hackers use psychology to entice users to click on malicious attachments or forms in order to obtain personal information. On the contrary, "Ethical Hackers" are professionals who hack into systems with permission and with no malicious intent. A Certified Ethical Hacking professional works like a hacker to identify the scope of potential risks that could disrupt the program's smooth operation. They conduct security judgment, red teaming, intrusion testing, and vulnerability assessments for the organization's security systems and programs.
The Certified Ethical Hacker (CEH) credential from EC-Council is a respected and trusted ethical hacking program that has become one of the best options for validating a professional's skills in penetration testing, vulnerability discovery, and evaluation in target systems. Certified professionals play an important role in protecting organizations' digital assets and infrastructures by identifying weaknesses and potential attack vectors to prevent data theft and misuse by malicious attackers.
The Importance Of Ethical Hacking
An ethical hacker's primary purpose is to keep sensitive data and information out of the hands of cyber criminals. It safeguards your organization from being threatened with extortion by those attempting to exploit flaws.
- The benefits of ethical hacking include: Organizations can identify security problems from the perspective of an attacker in order to enhance defenses.
- We can set up a secure network that prevents security breaches.
- Ethical hackers can protect national security by denying terrorists access to vital information.
- By offering secure goods and data, we can acquire the trust of our customers and investors.
What’s New In CEH V11
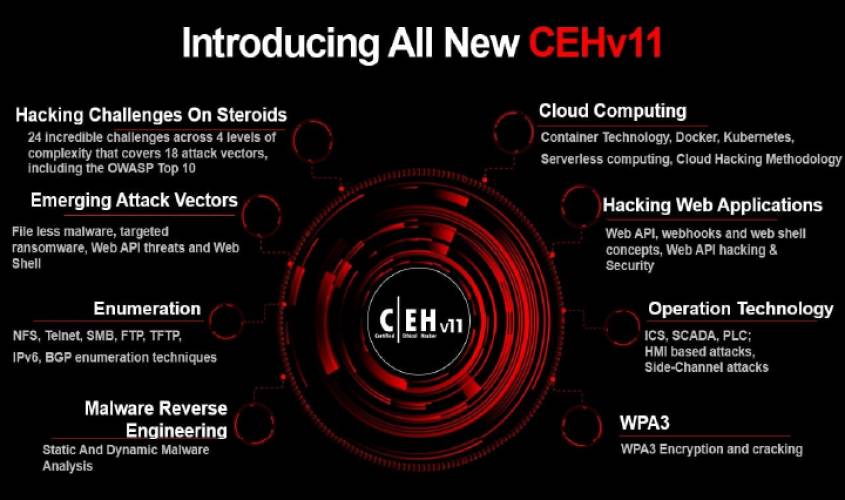
CEH v11 is more sophisticated, resilient, and thorough than ever before, with more hacking techniques, tactics, and tools covered than ever before.
CEH v11 now offers over 20 courses that students must study and comprehend; hacking tasks are included at the conclusion of each module to reinforce what is learnt. Cloud computing and remotely hosted solutions are two of the most prevalent technologies in the test.
CEH v11 focuses on 18 attack vectors, including the OWASP Top 10, IoT hacking, vulnerability analysis, APT, Fileless Malware, Web API Threats, Webhooks, Web Shell, OT Attacks, Cloud Attacks, AI, ML, and many others.
Become Top-Notch Analysts
Following considerable understanding in Ethical Hacking Training, Information Security professionals will have a developed knowledge of Ethical Hacking, which may benefit them in the future as an intrusion analyst, forensic analyst, or security manager, among other positions. As a result, people might strive to raise their level and position by improving their talents.
Learn How To Think Like A Hacker
The CEH certification provides teams with insights into cybercriminals' mindsets and emphasizes the truth that in order to defeat a hacker, one must think like a hacker. While fighting cybercriminals usually entails reacting to threats and events as they occur, understanding how these criminals conduct their assaults and developing strategies is even more important. Teams may take a proactive approach by learning how to think like a hacker, going beyond an organization's present security methods and regulations to identify areas that may be exposed to cyber-criminals.
Exciting Career Options
To become an ethical hacker, one must first understand the hacker's mind and then quickly sketch up the final scenarios for hacking a network/system/data, etc. After becoming a certified ethical hacker, you will be able to take on fascinating professions such as Computer Network (CND) Analyst, CND Incident Responder, CND Infrastructure Support, and so on.
In a nutshell, with the Certified Ethical Hacking training program, you may build the in-demand knowledge of ethical hacking, the many kinds of security dangers and comprehend the deep mentality of how a hacker benefits from the flaws. You’ll learn to practice the science of ethical hacking and much more! So, what are you holding out for? Register for the CEH v11 training program right now!
CEH With LABA
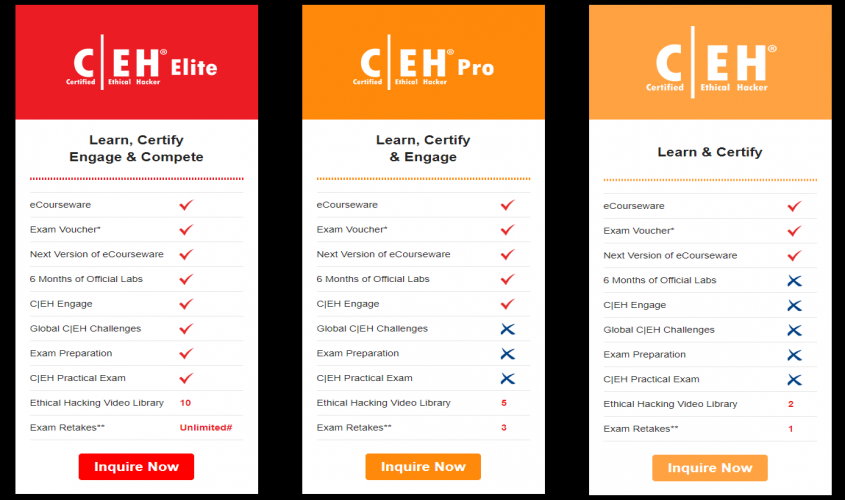
LABA is one of the major training companies with a pocket-friendly pricing. We encourage you to join us on an exciting trip with industry professionals to learn more about the Certified Ethical Hacker course.


.png)